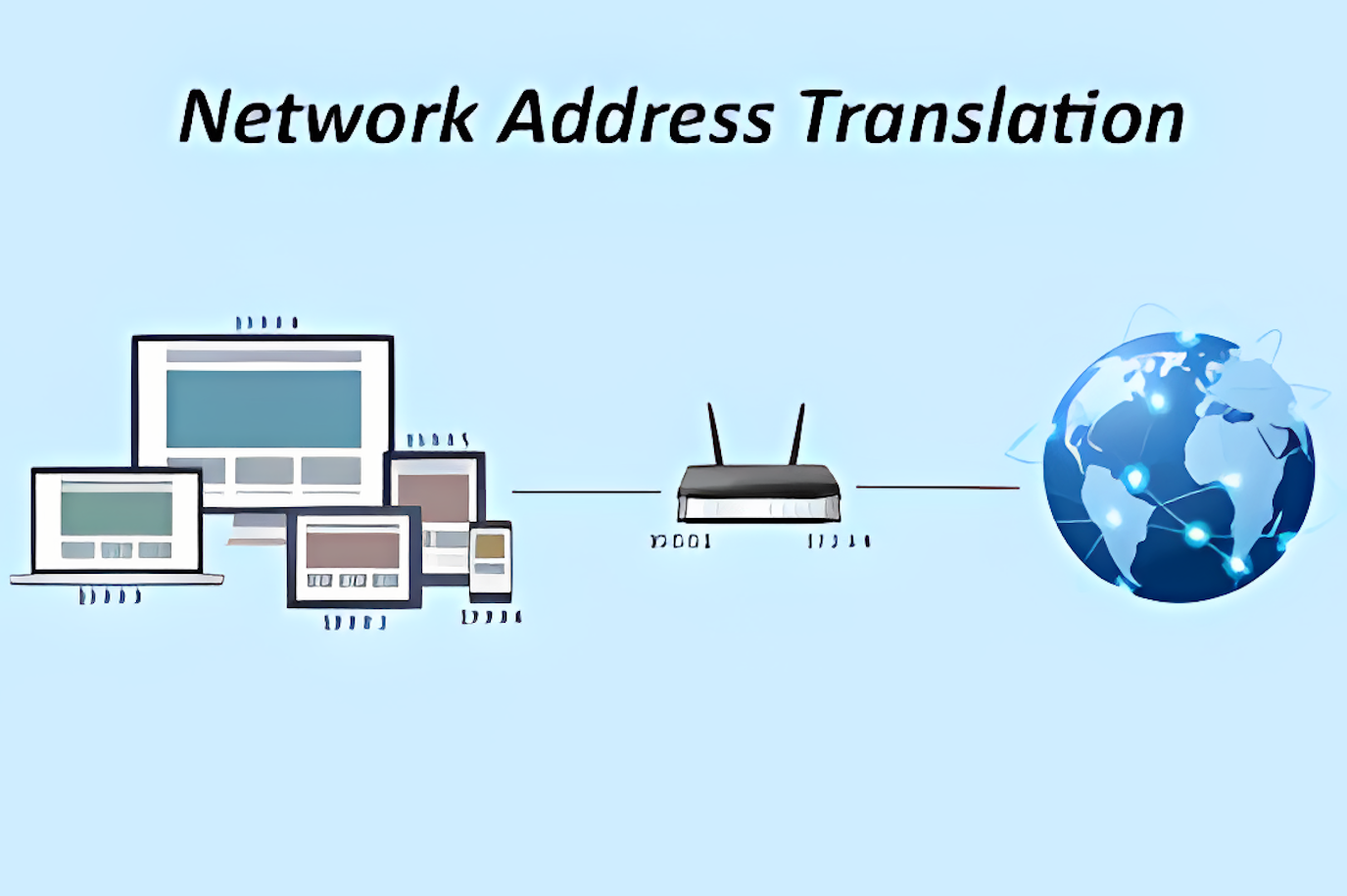
NAT
Allows devices on a private network to communicate with external networks using a single public IP address.
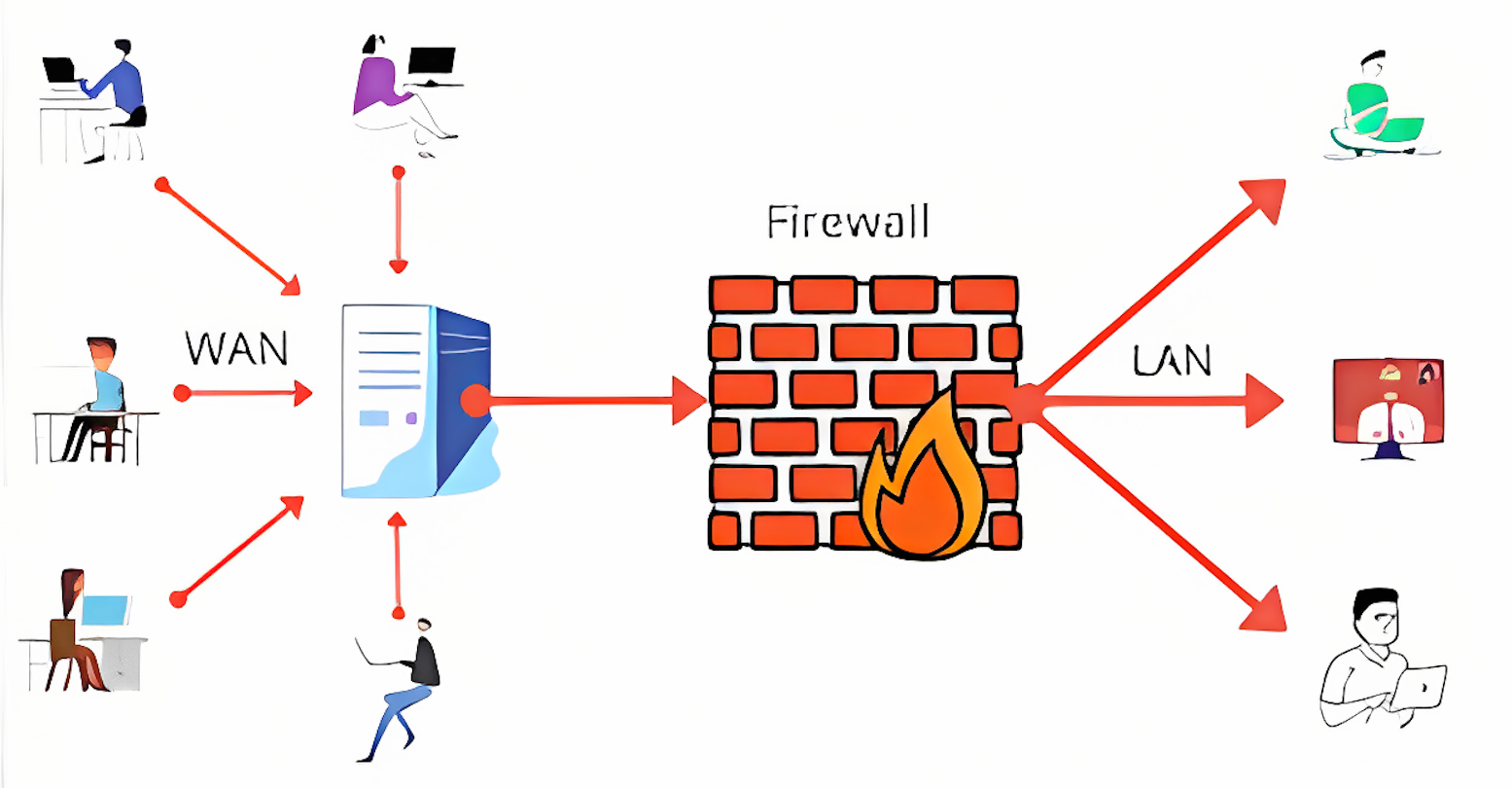
Firewall Rules
Control traffic flow between interfaces and define which packets are allowed or denied.

VPN
Securely connect remote users or offices to your network using IPSec, OpenVPN, or WireGuard.

IDS/IPS
Monitor and block suspicious or malicious traffic with tools like Snort or Suricata.

Dynamic DNS
Associate a dynamic IP address with a domain name for easy service hosting.
Traffic Shaping
Manage bandwidth to prioritize critical applications with QoS and traffic limits.

VLAN Support
Segregate network traffic for better organization and security.
Captive Portal
Control internet access for users on a specific network with authentication and time limits.

High Availability
Ensure uninterrupted service by using multiple firewalls in a failover configuration.

Logging and Monitoring
Gain insights into network activity with real-time logs and monitoring tools.

DNS Resolver and Forwarder
Resolve domain names for devices on the network efficiently.

Load Balancing
Distribute traffic across multiple WAN or server connections for reliability.

GeoIP Filtering
Restrict or allow traffic based on geographic locations.

Advanced Security Features
Protect the network with SPI, anti-spoofing, and rate limiting features.

Time-Based Rules
Automate rule activation based on schedules to manage access effectively.